Is Your Email Authentication Ready for 2026?
A Guide to DMARC Policy Updates
Email authentication is about to become more critical than ever. With new standards rolling out in 2026, businesses need to take a closer look at their DMARC policies to maintain email deliverability and protect their brand reputation.
Understanding DMARC Policies
Most organizations currently have their DMARC policy set to “none.” This setting, indicated by p=none in your DNS record, allows all emails that claim to be from your domain to pass through, even if they fail SPF and DKIM authentication checks. While these failed messages do generate DMARC reports sent to your designated email address, many organizations set up this monitoring and then forget about it.
The Three DMARC Policy Levels
None (p=none): Everything passes through regardless of authentication status. You’ll receive weekly reports about failed authentications, but no emails are blocked.
Quarantine (p=quarantine): Emails that fail authentication checks are treated with suspicion by receiving servers. These messages typically end up in spam or junk folders rather than being rejected outright.
Reject (p=reject): Failed authentication checks result in complete rejection. These emails never reach the recipient’s inbox and will show up as bounces in your email metrics.
Why 2026 Changes Everything
Email authentication requirements have been tightening since 2024, when Google, Yahoo, and Microsoft began enforcing stricter standards for bulk email senders (those sending 5,000+ emails per day). By 2026, these requirements have become the expected baseline for all serious email senders. Organizations with stronger authentication postures—particularly those with DMARC policies set to at least quarantine—are seeing better email deliverability and enhanced sender reputation.
Think of DKIM as your domain’s cryptographic signature. While SPF verifies that emails come from authorized IP addresses, DKIM adds a digital signature that proves the email hasn’t been tampered with in transit and genuinely originates from your domain.
Email providers increasingly favor senders whose DMARC policy is set to at least quarantine, recognizing them as organizations actively fighting spoofing and phishing attempts.
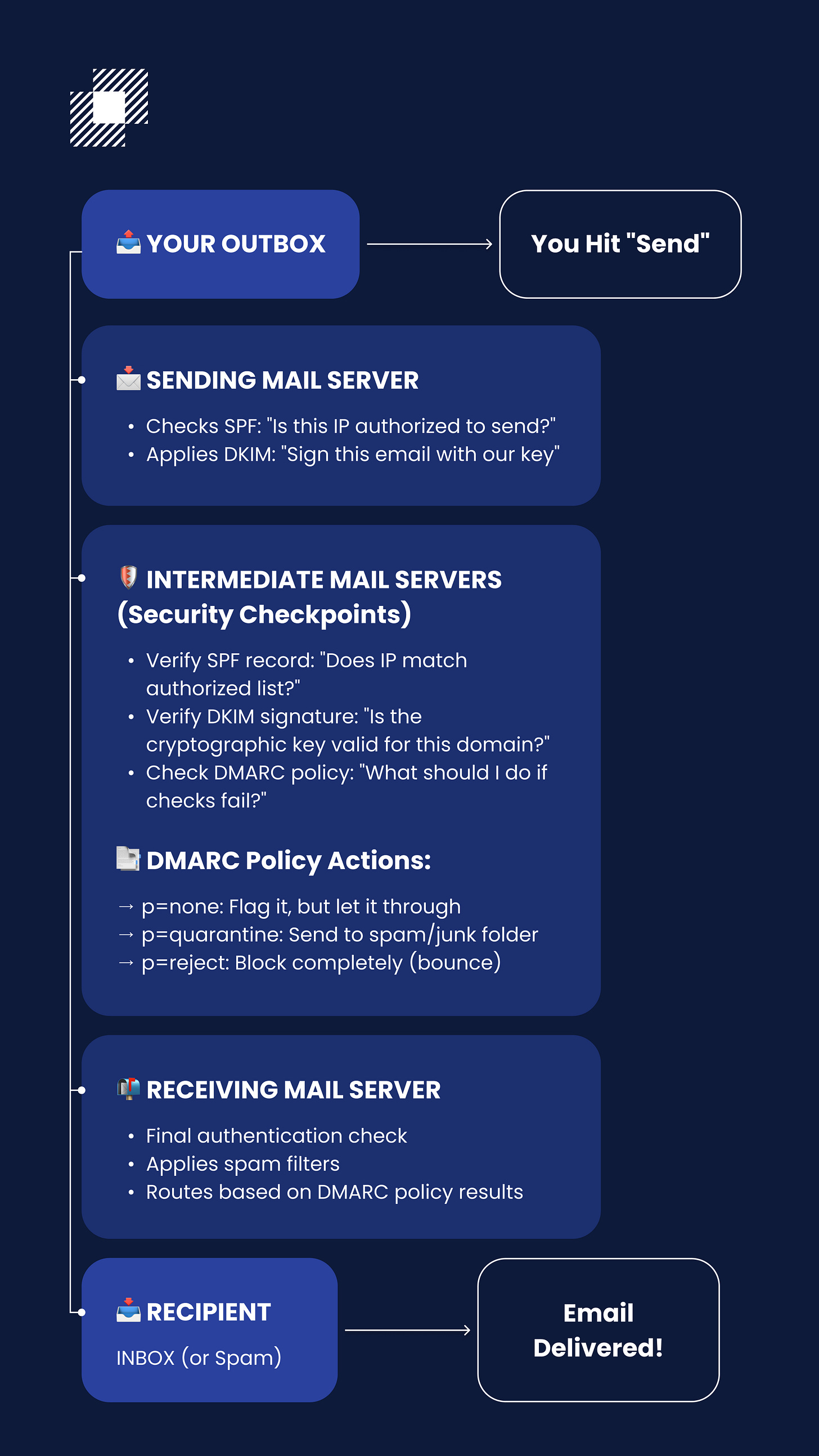
How Email Authentication Works
Understanding email’s journey helps explain why these policies matter. When you send an email, it doesn’t go directly to your recipient. Instead, it travels through multiple mail servers—digital post offices that sort, screen, and check your authentication records at every step. These servers analyze content, subject lines, and authentication credentials to determine whether messages are legitimate or spam.
Key Points:
SPF = IP Address authorization (”Is this IP address allowed to send from this domain?”)
DKIM = Message integrity with cryptographic signature (”Has this email been tampered with in transit?”)
DMARC = Policy enforcement (”What happens if SPF/DKIM fail?”) + alignment with the visible “From” address
Your DMARC record signals to these servers how to handle suspicious messages claiming to be from your domain. With a “none” policy, servers flag suspicious emails but let them through. With “quarantine,” they route them to spam folders. With “reject,” they block them entirely.
Making the Switch Safely
Here’s the recommended approach for updating your DMARC policy:
Start by monitoring your current DMARC reports for about a week. Make sure everything being flagged looks correct and that all legitimate emails are passing authentication checks. Only then should you switch from p=none to p=quarantine.
Don’t rush to p=reject. Without proper monitoring, you risk blocking legitimate emails from various parts of your organization—invoices from finance, contract renewals from legal, campaigns from marketing, and more. Any team that sends email on your behalf needs to be properly authenticated and aligned with your SPF and DKIM records.
Modular recommends staying at the quarantine level until you’re absolutely certain all legitimate services are authenticated and not failing verification. Moving to reject requires significant time and effort to ensure nothing important gets blocked.
Taking Action
The key takeaway: if your DMARC policy is currently set to “none,” upgrading to “quarantine” in 2026 is strongly recommended. This change will improve your email deliverability and sender reputation as industry standards continue to tighten, while still giving you the flexibility to monitor and adjust as needed.
The shift toward stricter email authentication is an ongoing industry evolution. Email providers have been gradually tightening enforcement since 2024, and by 2026, strong authentication has become baseline infrastructure for reliable email delivery.
Organizations that proactively improve their authentication posture will maintain better deliverability and protect their brand reputation in an increasingly security-conscious email ecosystem.